https://aka.ms/recoverykeyfaq – Microsoft Recovery Key FAQ

What is BitLocker? (aka.ms/recoverykeyfaq)
The BitLocker Recovery key will be required if Windows detects an unauthorized attempt to access files. It ensures that your information is protected from breaches.
This is also the case when you make changes to your system’s hardware software, firmware or firmware that BitLocker finds an untrustworthy attempt or attack. For security that is 100% secure, the owner of the device may require the BitLocker keys for recovery.
It is Microsoft’s security system to safeguard your data. In such cases, the device user has often been asked to visit windows.microsoft.com/recoverykeyfaq from another PC to get a recovery key ID.
You can also avail of comprehensive support on BitLocker encryption at aka.ms/recoverykeyfaq. Recovery keys are stored in Azure Active Directory. You can also locate it on the USB flash drive.
Device encryption with BitLocker is an effective method to protect yourself. You can block unauthorized users from accessing your important information and devices. To use this BitLocker password, you must understand all the operations and handling.
In addition, the BitLocker password is saved in Microsoft Account and retrieved accordingly in case of need. But, it’s crucial to be aware of the steps for finding BitLocker Recovery Key.
Exclusive Features:
- BitLocker can be used on external storage drives. All you require is authorization to gain access to encrypted drives.
- BitLocker uses TPM to offer the highest encryption and security for data.
- PC startup is tested and verified through Windows Trusted Platform Modul (TPM). This initial assessment blocks Boot Sector Viruses as well as unauthorized access.
- The TPM chip is a unique chip that protects and monitors your hardware, software, and firmware for sudden and unauthorized modifications. The TPM will automatically switch your computer into a restricted mode in the event of unauthorized changes or attempts at access.

How to Enable BitLocker for Drive and Device Encryption?
Systems Requirements
- The system BIOS must be compatible with the latest UEFI options. This will ensure Secure Boot mode in BIOS.
- BIOS’s Trusted Platform Module (TPM) must be version 1.2 or greater.
- If BitLocker doesn’t have access to TPM hardware, it searches for a startup code that can be stored on a removable device.
- Make sure your hard disk is divided into two parts, with one section using the NTFS file system.
- It requires an additional hard drive, which is not encrypted, and a minimum of 1.5 GB of storage space.
- BitLocker does not assist dynamic disks.
Common methods of enabling BitLocker in the OS So, please adhere to the steps you prefer:
Windows 7:
- Open the Start Menu, click on the Search Box and search for “Manage BitLocker”.
- Start My Computer, right-click on the drive, then select to turn on BitLocker.
- Start Menu > Control Panel» System and Security > > > BitLocker Drive Encryption.
Windows 10:
Start Menu Control Panel – Security and System BitLocker Drive Encryption.
Or:
In the Start menu -> Settings in the box for search, enter “Manage BitLocker” Choose Manage BitLocker.
- Next, click Turn on the BitLocker button to select your preferred backup option and save the recovery key.
- Select the required Encryption option.
- Run the BitLocker system check.
- Restart the system to start the BitLocker encryption system.
What is BitLocker Recovery?
BitLocker, also known as the Microsoft recovery key, is generated automatically whenever you attempt to decrypt an encrypted drive with BitLocker. Microsoft recovery keys are used to decrypt or unlock the encrypted drive in the event of a hard drive or motherboard issue, or even password misfortune.
- The BitLocker recovery key is a particular 48-digit code to unlock an encrypted device.
- Microsoft lets you save and save your password when creating it on account of your Microsoft account.
Apart from Microsoft account recovery via windows.microsoft.com/recoverykeyfaq, other options to recover your BitLocker Key are printing out where you noted the Recovery key at the time of activation, USB Flash Drive plugged in the locked PC, and Azure Active Directory account. Contact your system administrator to learn more about the other methods of recovery.
BitLocker Recovery key storage options
Keys for recovery can be saved in various methods based on the type of Windows installed. This list provides choices for saving keys for every operating system version. It also could help locate keys that have been saved (if there is one):
For Windows 7:
- A key may be saved to a USB flash drive
- A key may be saved as a file (Network drive or other location)
- A key may be physically printed
For Windows 8.1:
- A key may be saved to your Microsoft account (Access your Microsoft account from a different computer to retrieve the key)
- A key may be saved to a USB flash drive.
- A key may be saved as a file (Network drive or other location)
- A key may be physically printed.
For Windows 10:
- Keys can be stored on account of your Microsoft account (search Keys to Recovery with BitLocker to find to retrieve the code).
- If you own a modern device that has auto-encryption, your recovery key will likely be stored in the account of your Microsoft account. For more information, refer to the device encryption feature on Windows 10
- When the gadget was initially set to go live in the past or a different user enabled BitLocker protection, the recovery key might be stored in the user’s Microsoft account.
- The key can be stored on a USB flash drive (Plug the USB flash drive into your locked personal computer and follow the directions. If you have saved your key in text files in the drive, use an alternative computer to open the file.)
- A key could save to an Azure Active Directory account (for work-related PCs, where you log in with the Azure Active Directory account, to obtain your recovery keys, check the details for your device on the details of your Microsoft Azure account)
- A key can be saved as a document (Network drive or another location)
- A key could be printed physically.
Where can I find my BitLocker recovery key?
BitLocker ensured that the recovery key was stored before activating the protection. There are a variety of places where your recovery key could be, based on the selection made during the activation of BitLocker:
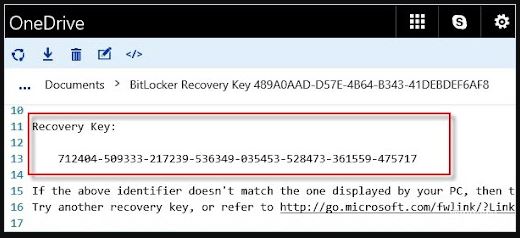
In your Microsoft account: Sign in to your Microsoft account on a different device to locate your recovery key. If you own a modern device that can support automatic device encryption, your recovery key is likely to be stored in the account of your Microsoft account. For more information, refer to the device encryption feature within Windows.
NOTE: If the device was installed or a different user-activated BitLocker protection, The recovery key could be stored in the account of the user’s Microsoft account.
On a printout: You may have printed your recovery keys when BitLocker activated. Find the place where you store important documents connected to your PC.
On a USB flash drive: Plug the USB flash drive into your computer and follow the directions. In the event that you have saved your key in a text file on the drive, you can use an alternative computer to open it as a text file.
In an Azure Active Directory account: If your device was ever logged into an organization using an email account for a school or work account, your recovery code could be stored in the company’s Azure AD accounts associated with the device. You might be able to access it from your device or get in touch with the system administrator to access your recovery key.
Held by your system administrator: If your gadget is linked to a domain (usually an educational or work device), ask your system administrator to provide the recovery key.
Why is Windows asking for my BitLocker recovery key?
BitLocker is the Windows encryption technology that shields your data from unauthorized access by encrypting your drive and needing one or more forms for authentication before allowing access to it.
Windows will require a BitLocker recovery key whenever it detects an unauthorized attempt to access your information. This additional step is an extra security measure designed to protect your data and protected.
This could also occur if you modify your firmware, hardware or software that BitLocker can’t distinguish from an attack.
In these instances, BitLocker may require the additional safety of the recovering keys even when the user is a legitimate gadget owner. This will ensure that the person attempting to unlock the data is legally authorized.
How was BitLocker activated on my device?
There are three standard methods to use BitLocker to begin protecting your device:
The device you are using is a contemporary device that meets the required specifications to enable encryption automatically: In this case, your BitLocker recovery key is saved automatically on the account on your Microsoft accounts before activating the protection.
The administrator or owner of your device has activated BitLocker security (also known as device encryption on certain devices) via the Settings App or Control Panel: In this case, the user who activated BitLocker chose which location to store the keys or (in the instance of encryption on devices) it was saved automatically into your Microsoft Account.
A school or work company responsible for your devices (currently or previously) has activated BitLocker security for your gadget: In this case, the organization could have your BitLocker recovery code.
BitLocker is activated only via or on behalf of a person who has full control over your devices, regardless of whether it’s you, another user or an entity managing the device. The BitLocker installation process requires the creation of a recovery key before the moment of activation.
How to Reset BitLocker Password?
The simplest ways to change your password include:
- Right-click on the device and click “Manage BitLocker” on your pop-up menu.
- Next, choose to change or reset your password.
- Click on “Reset an account that was forgotten”. This will allow you to avoid giving the old password you may have lost.
- Make sure you type your new password twice and then keep all modifications.
How to Make BitLocker Encryption Strong?
Enabling BitLocker encryption on your device isn’t enough to secure your device against unauthorized or fraudulent access. It is equally crucial to make sure you adhere to certain security quotients.
- Do not save your BitLocker keylocks or passwords locally.
- Windows stores BitLocker 48-digit recovery keys by saving it as a straightforward text file when you select to save it; however, to be sure of security, try saving the recovery key in the Microsoft email that you use.
- Instead of having the key locked in a printed form, it’s always safer to store it wherever you can save secure access.
- Suppose you plan to utilize third-party password management software such as 1Password and 1Password. Be sure to create a secure password comprised of alphabets, upper and lower case, and special characters that are all used together.
Also Check:
- Aka.ms/accountsettings
- aka.ms/authapp
- Aka.ms/mfasetup
- Aka.ms/myrecoverykey
- Aka.ms/remoteconnect
- Aka.ms/xboxsetup
- aka.ms/recoverykeyfaq
What causes BitLocker recovery?
The following list of some examples of the specific circumstances that can trigger BitLocker to be in recovery mode while trying to launch the drive of the operating system:
- For PCs using BitLocker Drive Encryption and other devices such as tablets and phones that employ BitLocker Device Encryption solely, the device will restart and enter BitLocker Recovery if the threat is identified Mode. Administrators can set the Interactive logon: Machine account lockout threshold Group Policy setting located in \Computer Configuration\Windows Settings\Security Settings\Local Policies\Security Options in the Local Group Policy Editor. Or they can use the MaxFailedPasswordAttempts policy of Exchange ActiveSync (also configurable through Microsoft Intune) to limit the number of failed password attempts before the device goes into Device Lockout.
- On devices with TPM 1.2, Modifying either the firmware or BIOS boot device’s sequence triggers BitLocker recovery. However, devices running TPM 2.0 don’t begin BitLocker Recovery in this scenario. TPM 2.0 does not view the change in the boot device’s order as a security risk because there is no risk to security. After all, the OS Boot Loader is not affected.
- Insert the DVD or CD drive before the hard drive is in the BIOS boot order, and then insert an optical disc or CD.
- Inability to start a network drive before starting from the hard drive.
- Docking or unloading the portable computer. In certain instances (depending on the manufacturer of the computer and BIOS), the docking status for the laptop computer is a part of the system’s measurement. It must be consistent with verifying the system’s status and with unlocking BitLocker. Therefore, if a laptop device is docked to its computer while BitLocker is on and locked, it may have to be connected to the docking station once it is locked. In contrast, if the portable computer isn’t attached to the docking station once BitLocker is on, it could be disconnected from the docking stations after it is locked.
- Modifications made to the NTFS partition table in the disk include deletion, creation or resizing of the primary partition.
- Inputting the Personal Identification Number (PIN) incorrectly enough times to activate the anti-hammering mechanism in the TPM. Anti-hammering logic can be described as implemented in hardware or software, which increases the cost and difficulty of an attack using brute force on PINs by refusing to accept PIN numbers until time has passed.
- By turning off the support to read the USB device from the pre-boot environment of your BIOS, or the firmware for UEFI, if you’re using USB-based devices instead of TPM.
- The TPM can be turned off, disabled, deactivated, and cleared TPM.
- Upgrades to critical components of the early startup for the initial startup, like BIOS, UEFI or firmware update, can cause the measurement of the boot to alter.
- The forgetting of the PIN after PIN authentication is activated.
- Update option firmware for ROM.
- Upgrade of TPM firmware.
- The process of adding or removing hardware. for instance, inserting a new card into the computer, for example, some PCMIA wireless devices.
- Inserting, removing or completely depleting the charge of a battery for smart devices on the portable computer.
- Modifications in the master boot records on disk.
- Modifications made to boot managers on your disk.
- Hiding the TPM’s information from operating systems. Certain BIOS or settings in UEFI can stop the enumeration process of the TPM by an operating system. If implemented, this feature will make the TPM unreadable by the operating system. If it is not visible, BIOS, as well as UEFI secure start, are turned off. The TPM will not respond to any commands issued by the software.
- A different keyboard cannot properly enter the PIN or whose map of the keyboard does not correspond to the map of keyboards used by the pre-boot system. This issue can hinder the entering of enhanced passwords.
- Editing the platform configuration registers (PCRs) used in TPM is a way to modify the TPM verification profile. For instance, including the PCR[11 will result in BitLocker not detecting most modifications to BIOS settings, which would cause BitLocker to be in recovery mode even if non-boot critical BIOS settings are changed.
Note: Some computers are equipped with BIOS settings that don’t allow measurements of certain PCRs, for example, the PCR [2]. The change in this setting in BIOS could result in BitLocker switching to recovery since the PCR measurement would differ.
- Transferring the BitLocker-protected drive to the new computer.
- The motherboard is upgraded to a new model with the latest TPM.
- It is possible to lose the USB flash drive with the startup key after the startup key authentication is disabled.
- Failure to pass failing the TPM self-test.
- The BIOS or UEFI-based firmware or an option ROM component isn’t compatible with the applicable Trusted Computing Group standards for a client-side computer. For instance, an uncompliant application could capture volatile data (such as time) in TPM measurements, which can cause different measurements for each startup and lead BitLocker to go into recovery mode.
- Change the user authorization of the root storage key in the TPM to a non-zero number.
Note: The BitLocker TPM initialization process sets the value for authorization to use to zero. Therefore, a new user or process must have expressly altered this value.
- Enable the integrity check on code or activate test signing in Windows Boot Manager (Bootmgr).
- By pressing the F8 key or F10 keys during the boot procedure.
- Add-in cards can be removed or added (such as network or video cards) or updated software on the add-in cards.
- Utilizing the BIOS hotkey during boot time to alter the order of booting to something different from that of the drive.
Note: Before beginning the recovery process, we suggest you identify the cause of your recovery. This could help in preventing the issue from happening later on. For example, if you find that an attacker has altered your computer through accessing it physically, You can set up new security rules to monitor those who are physically present. Once the recovery password is used to gain access to the computer, BitLocker will then re-encrypt the encryption key according to the measured components’ actual values.
For planned scenarios, like an upgrade of firmware or hardware, it is possible to avoid starting recovery when you temporarily stop BitLocker protection. Since suspending BitLocker makes the drive completely secure, administrators can quickly return to BitLocker protection when the job is completed. The suspend and resume feature also resets the encryption key without the need to enter an additional recovery code.
Note: If it’s suspended, BitLocker will restore protection once the computer is rebooted, except if it is determined that a reboot count must be specified by using the manage-bde command-line tool.
Suppose software maintenance needs the computer to be restarted, and you’re using two-factor authentication. In that case, you may activate BitLocker Network Unlock to serve as the second authentication factor if the computer does not include an on-premises user who can offer an additional authentication method.
Recovery is described in the situation of unplanned or unintentional behaviour. However, you can create a recovery scenario as an intended production situation to control access control.
For example, suppose you transfer laptop or desktop computers to different departments or employees of your organization. In that case, you may make BitLocker go into recovery before the computer is handed over to an individual who is a new user.
Latest Guides
Aka.ms/accountsettings – How to Fix aka.ms/accountsettings
Aka.ms/accountsettings – The aka.ms/accountsettings error is a notification that is sometimes displayed to Minecraft users who are
Aka.ms/mfasetup – Set up your Microsoft 365 Sign-in for Multi-factor Authentication
Aka.ms/mfasetup – Set up your Microsoft 365 Sign-in for Multi-factor Authentication
Aka.ms/myrecoverykey – Where can I find my BitLocker recovery key
Aka.ms/myrecoverykey – Where can I find my BitLocker recovery key
Aka.ms/remoteconnect Error – Fixed [100%]
Aka.ms/remoteconnect Error – Https Aka Ms Remoteconnect Not Working? (Easy FIX!)
How to breed horses and mules in Minecraft to start your own farm ?
breed horses in Minecraft allows you to be just about anything. You can be a mighty warrior, a brave cave-diver, or just a farmer.
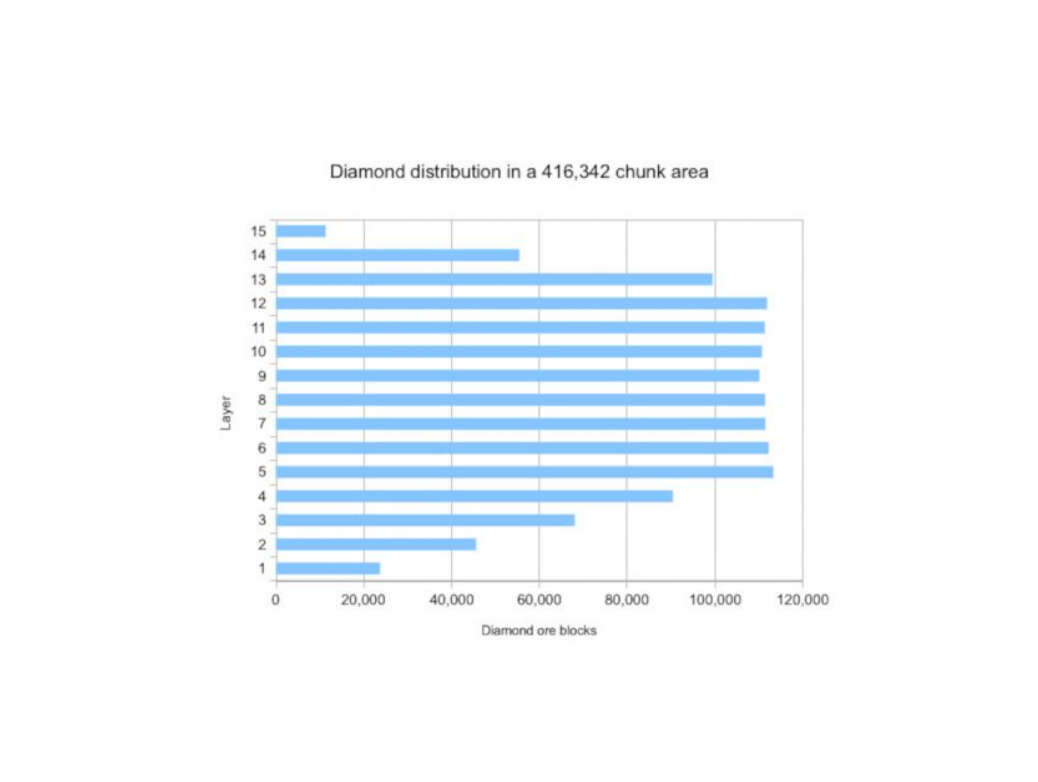
Diamonds In Minecraft – How to find diamonds in minecraft ?
diamonds in minecraft: This is how far you will have to dig to find Minecraft's diamond level in the most recent update. Also, thi